Between increasing cybercrime and meeting regulatory standards, many financial institutions are concerned about their security posture. One of our clients, a $30 billion bank with locations in multiple U.S. states, was no different.
They wanted to boost endpoint security by shutting-down all vulnerabilities in their environment, which included 5,042 workstations and nearly 1,000 servers.
Over 50% of those workstations were operating on a version of Windows 10 that wasn’t going to be supported much longer. Endpoints were across the board with different Windows OS versions. Servers were consistently updated, but required manual intervention to finish patching. These factors were causing a lack of security and efficiency for the team and environment.
In 2022, their senior management made endpoint security protection a company objective with ongoing weekly oversight, and hired us to help.
Our main objectives were to:
- Bring all workstations to the latest version of Windows 10 and get them fully patched.
- Fully patch servers as necessary
- Automate all software updates, not just patches labeled high-security and critical, including 3rd party apps
Streamlining Patch Management With Configuration Manager
Our first step was tackling the workstations. The large number of workstations needing to be upgraded proved a challenge, especially because not disrupting end users during the update was a high priority. Updates needed to be done at night when bank employees were at home.
Configuration Manager was already partially deployed which gave us a great starting point. We also have a proprietary methodology called InPlace Upgrade Hydration Kit that proved useful in this situation. InPlace Upgrade Hydration Kit can target large groups of endpoints and update them during scheduled time blocks, whether or not they are connected to the corporate network.
We used the InPlace Upgrade Hydration Kit along with Configuration Manager to update all 5,042 workstations during the bank’s off hours. We also implemented automation for all future updates.
The servers, on the other hand, didn’t need to be upgraded across the board. They needed an automated patching process. We created this process.
A 3rd party patching solution was also installed. We coordinated with the in-house security team to identify at-risk products. Then we then set up Configuration Manager integrated with Patch My PC to perform third party updates ongoing.
A Secure & Automated Modern Patching Environment
As a result of the solution we implemented, over five thousand workstations were upgraded to the most recent version of Windows 10. They are easier and less labor intensive to maintain now that they now longer require individual updates per OS.
All workstations and servers have an automated patching process that includes third-party patches. Manual OS updates are no longer required. While there are still some internally-managed servers that could use improvement, the bank is dedicated to the process. They continue to work on up-leveling their own internal efforts.
The bank has improved their data collection process to find rogue devices. They have also deployed agents to improve the frequency and accuracy of reporting.
A ~90% Significant Drop In Outstanding Vulnerabilities
A vulnerability assessment tool managed by the bank indicated a large decline in outstanding vulnerabilities, largely as a result of our work. This measurement included both Microsoft and 3rd party software components. To date, the largest decline has been in the Microsoft space where we manage the devices.
Although the number of assets being tracked increased from 5,700 to 6,210 in the last 3 years, the bank has continued to see steadily declining risk score:
- July 2021: 290,000,000
- July 2022: 58,068,192
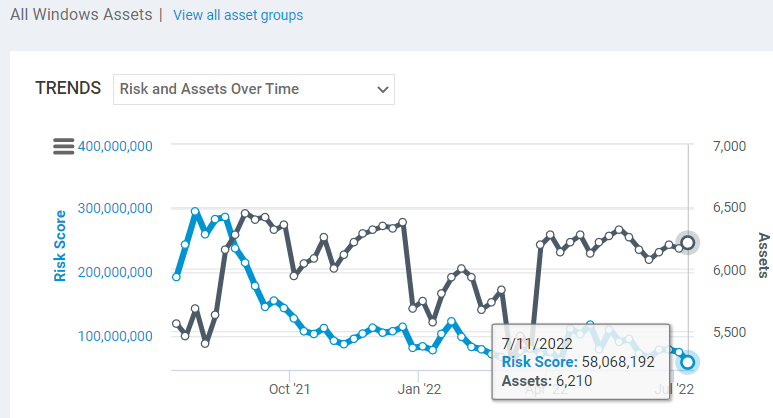
According to one of the bank’s Info Security Analysts, Model was a “key player” in the reduction of these vulnerabilities.
The trend continued, and as of January of 2023, the risk score has dropped to less than 30,000,000. We’re now working hard to ensure sustainability by attacking any vulnerabilities discovered in ongoing scans, as well as ensuring monthly updates are deployed and remediated to keep the risk score low.
Overall, the security posture of the bank has improved drastically, company higher-ups feel more secure, and there’s significantly less work for internal IT team.