Troubleshooting Microsoft Azure AD Sync Issues
First, make sure that the device is properly joined to Microsoft Azure Active Directory. If the device is on-premises, make sure that it’s hybrid joined. If it’s cloud based, make sure it’s Azure-joined. Azure AD devices will not work as part of co-management. Keep that in mind whenever you’re trying to troubleshoot devices. Hybrid joined or Azure-joined are the only two supportive types. Any of the internet-facing devices that are Azure AD joined will require a CMG if you want to implement co-management for internet-facing-only devices as well.
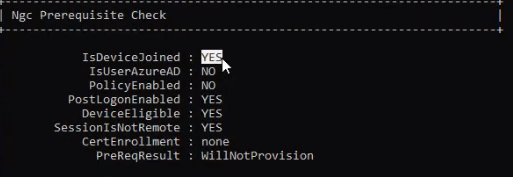
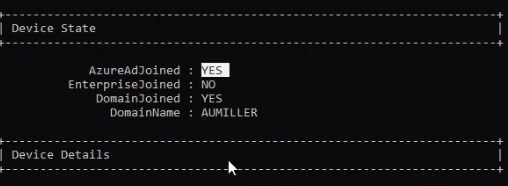
Typically, the way you can check this is if you open up Command Prompt on the device and type in dsregcmd /status. Scroll up to the top of your results and you’ll see the status of your device. For example, in this case, the Azure AD join is set to ‘No’ and the domain join is set to ‘Yes’.
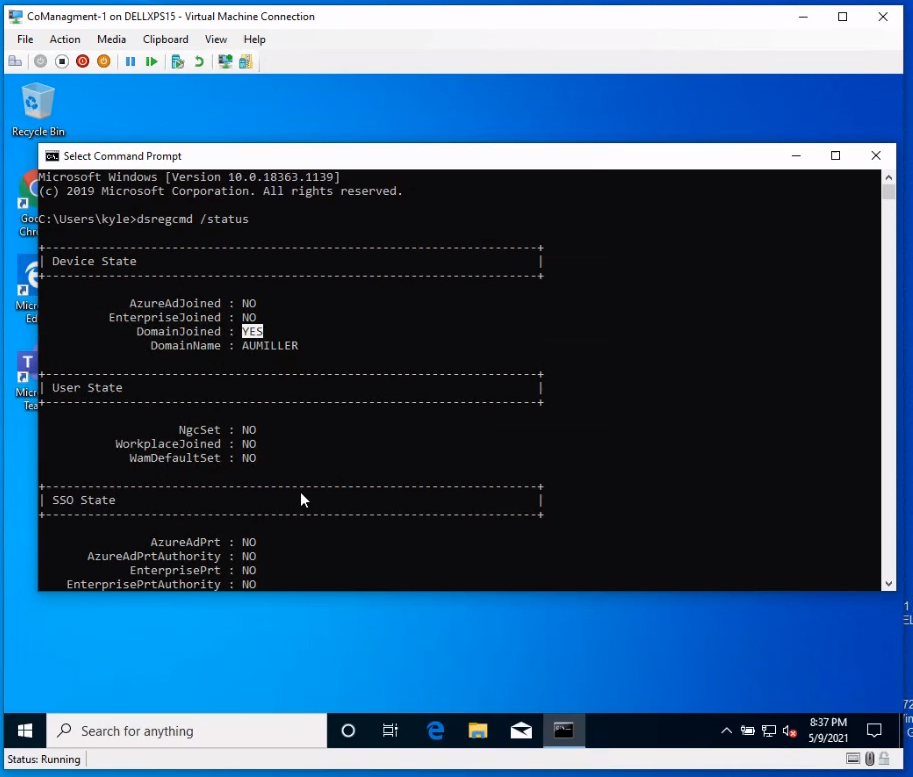
If you scroll down a little bit further, if the device is not connected it will say No under, “Is device joined” and “User Azure AD joined.”
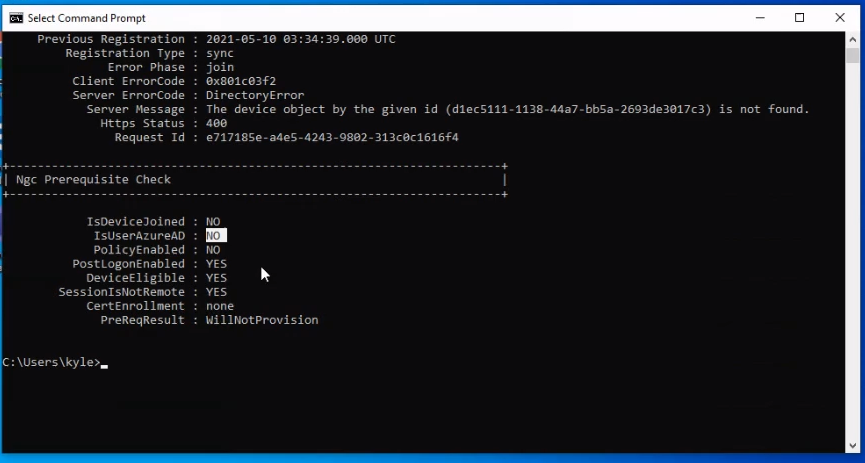
This is really the first step that I take a look at whenever I’m troubleshooting a device.
The next step is to also check your Azure AD portal and see if the device name is showing. First, find out what your computer name is. To do this, simply type in echo %computername% into command prompt.
Copy that name and come out to the Azure AD portal.
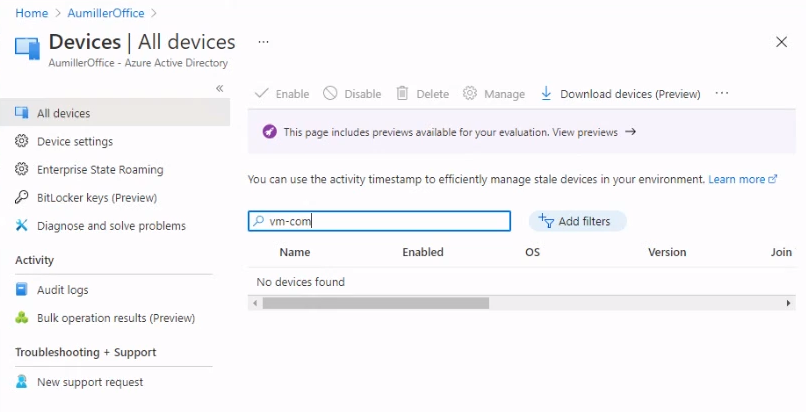
If you do not see that device as being registered into Azure AD, that’s the first step in identifying what is actually going on with the device.
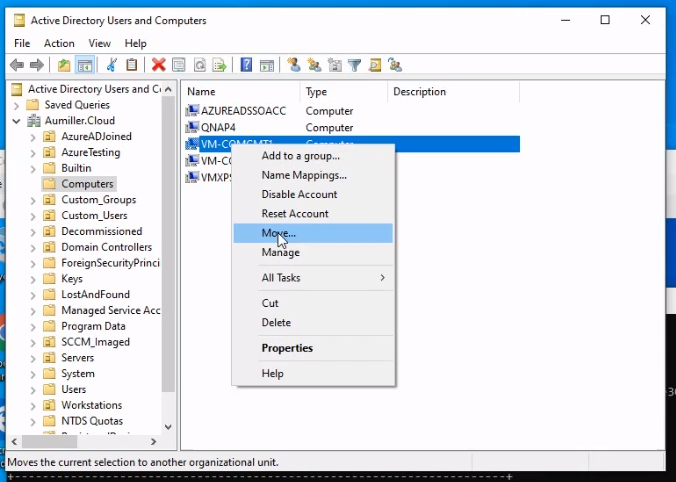
If it’s not joining, first what you want to do is move the device to a workstation’s organizational unit which you know is synced. To do that, open up Active Directory Users and Computers and right click the device. Click the Move option and select an organizational unit you know is synced.
Now restart your device.
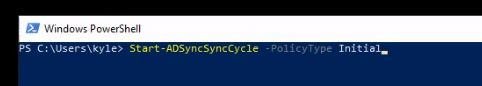
Next you want to kick off a sync in Azure AD Connect to take a look at what devices have changed.
Given a few minutes, that device should now appear on your Azure AD Portal.

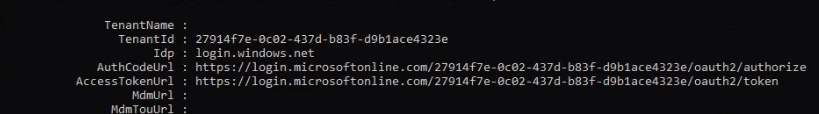
Now that device has synced, it shows a registration time, and it shows that it is hybrid Azure AD join, if you run your DS Reg command again, it should now say the devices is Azure AD joined, show a tenant ID, and, below again, that the device is joined.
We suggest restarting again just to make sure that the join actually worked properly. To double check, go back to your Azure AD portal. If nothing is showing pending there, that is a good sign.
Troubleshooting Microsoft Intune Sync Issues
If your device is not registering in Intune, we next want to figure out why this is not connecting which would then enable Intune co-management.
First, check to make sure the device is not connected by going to endpoint.microsoft.com. Once everything connects, you should see your device pop up in here as well.
If it does not connect, the first step in troubleshooting from here is figuring out why the device did not automatically enroll in Intune.
First you want to check your Co-Management Handler log. This will tell you if your settings have actually been created yet.
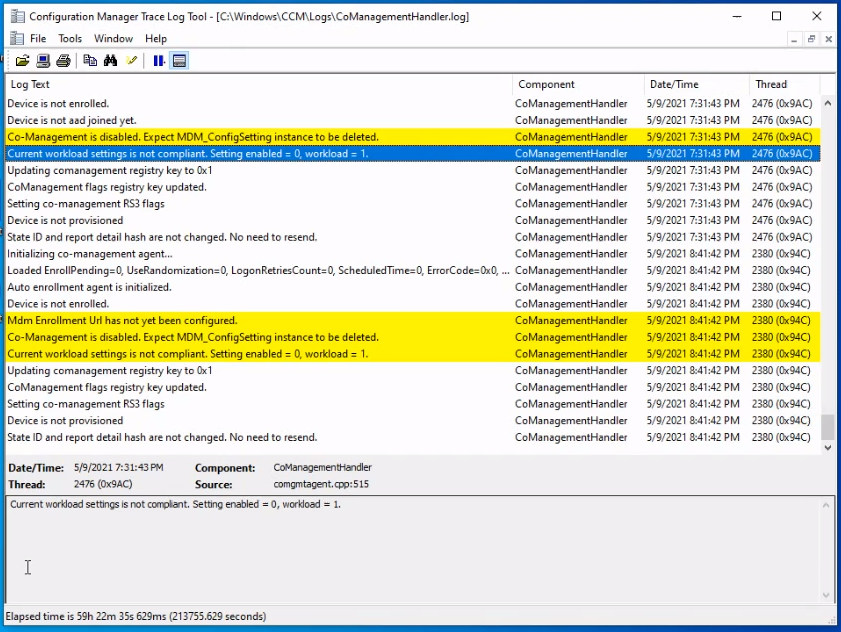
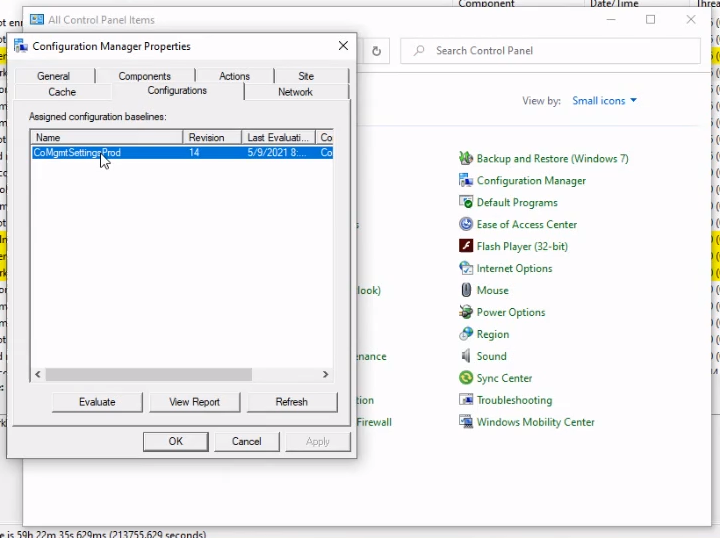
To fix this, first open up your configuration manager client via the control panel. Go into Configuration Settings. Click Evaluate, which could start to create activity in the Co-Management Hander log.
If you see your device is still not provisioned, next we’ll take a look at the SCCM console at how your configuration settings are set for co-management.
Open up your SCCM console and click Administration in the bottom left of the window.
Then click Co Management under the Cloud Services tab.

Right click your co-management instance and select Properties.
Check under the Enablement tab to make sure that your Automatic Enrollment is set correctly.

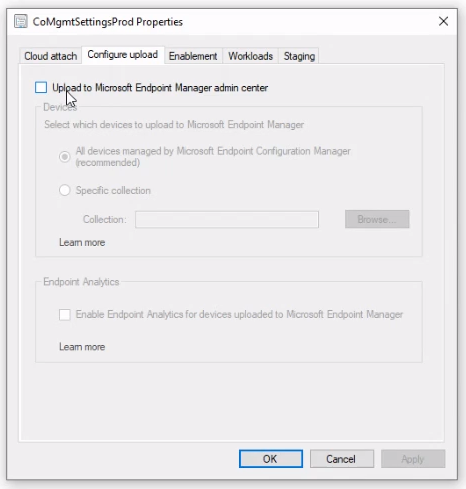
You also want to check under the Configure Upload tab to make sure it is configured to automatically upload all devices. This is a newer feature within the past few releases of SCCM.
Whatever you choose to configure the upload as, you want to make sure that your device is added to that specific collection. To do this, find the device collection that you have set to automatically upload. Right click on it and select Add Resources.
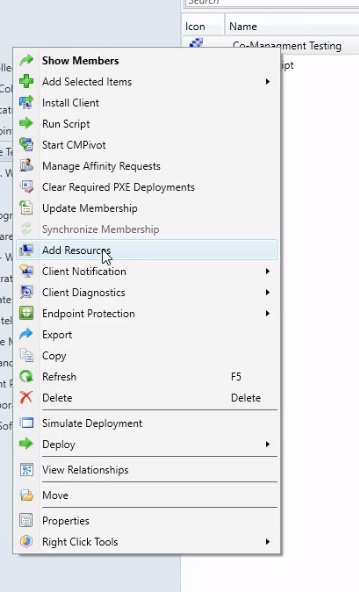
Type in the name of the resource under the Name string contains: text box. Click search, and your device should pop up. Select it and click the Add button to add it to the collection.
Validate that that device is showing appropriately in this collection by double clicking to open it and see the devices it currently contains.
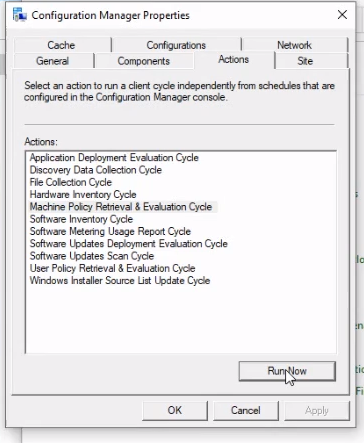
After you complete this process, the next thing you want to do is to configure your baselines. Go back to your Configuration Manager Properties and click the action tab. Select the Machine Policy Retrieval & Evaluation Cycle option and select run.
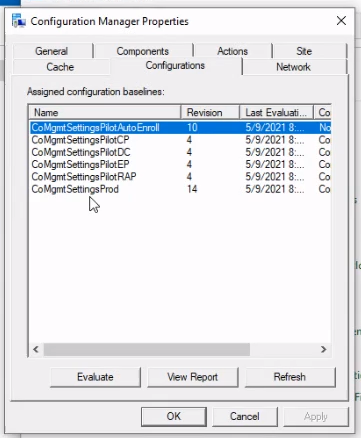
You should see a few more options under the Configurations tab.
Your device should also read provisioned and Enrolled in MDM in Configuration Manager.
It should appear in your Microsoft Endpoint Manager console in a few minutes as well. Once it does, it will be set up to be co-managed.
Using SCCM to Adjust Co-Management Workloads
In your SCCM console co-management settings you have what are called workloads. This is where you select which responsibilities you want Intune and Configuration Manager to be responsible for. You can set responsibilities for:
- Device configuration
- Endpoint protection
- Resource access policies
You can also set staging for compliance markers as well. If you’re looking at specific devices that you might have to test compliance policies, device configuration, endpoint protection and resource access policies, you can adjust those workloads as needed.
For example, if you want to assign update policies to configuration manager or Intune, move the slider to that side. And under the staging group, select the staging group you want to use.
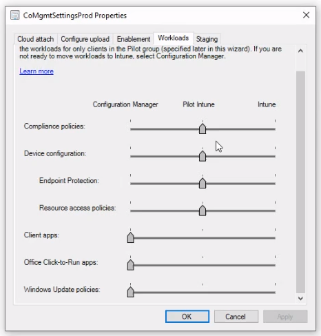
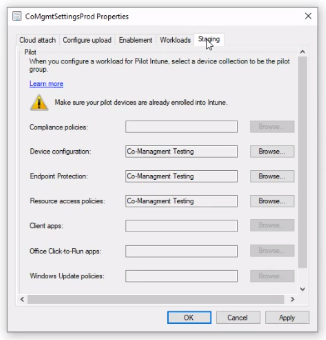
If you’re ever having issues with devices not receiving policies that they should be, check which collection these devices are actually in and where the slider is actually at in these settings.
Troubleshooting Device Compliance Issues With Windows Endpoint Manager
Whenever you’re trying to troubleshoot issues especially surrounding compliance, you want to start by looking at the device compliance and device in Windows Endpoint Manager.
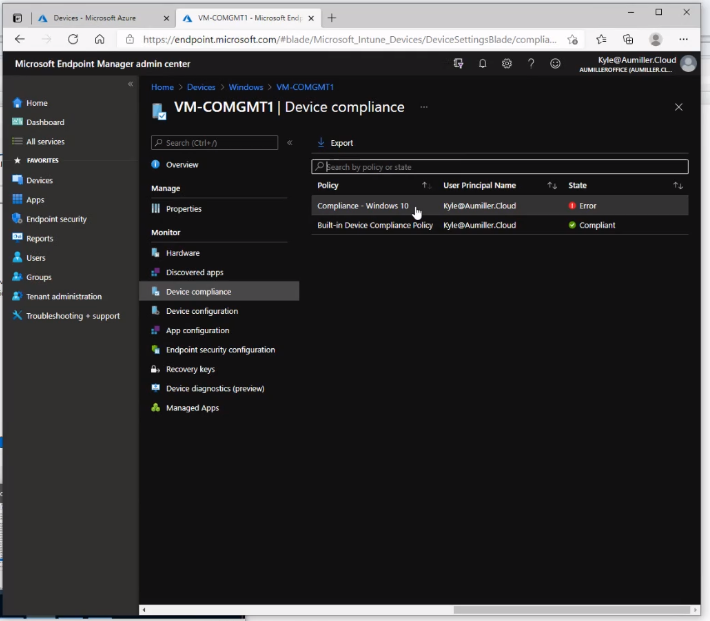
When you’re troubleshooting compliance issues, come out here and look and it’ll tell you exactly what’s going on. It shows an error code.
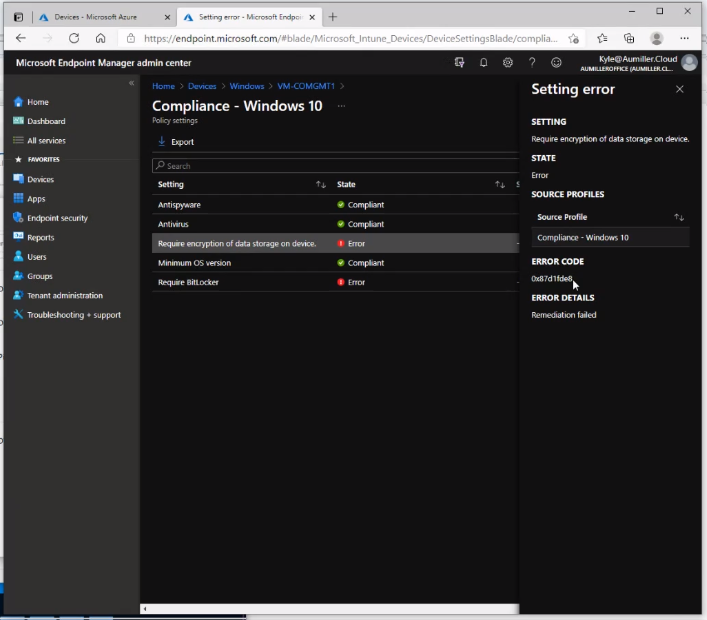
The next place you can go and look is under computer management. There are logs out here that will show you everything that’s going on.
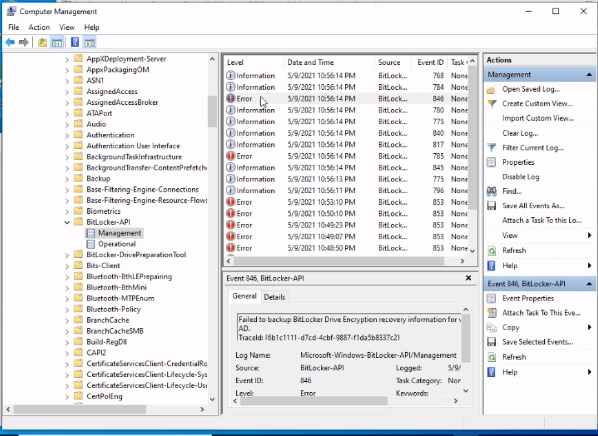
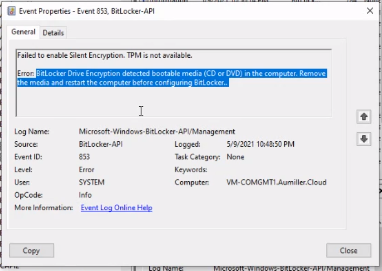
Here you can see the issue with it. As I was saying earlier, BitLocker does not like CD-ROM drives in the disk drives.
Once you fix the problem, this compliance policy will still show that there is an error here. Don’t be alarmed. Restart the device. Specific parts of the compliance policy specifically dealing with encryption will not actually re-evaluate until that device is restarted.
For more troubleshooting on the devices if you want to find out what workloads are managed by this device, you look at the device through the Endpoint Manager Admin center. Go to the overview of the device and you can find out what workloads into manages for the specific device.
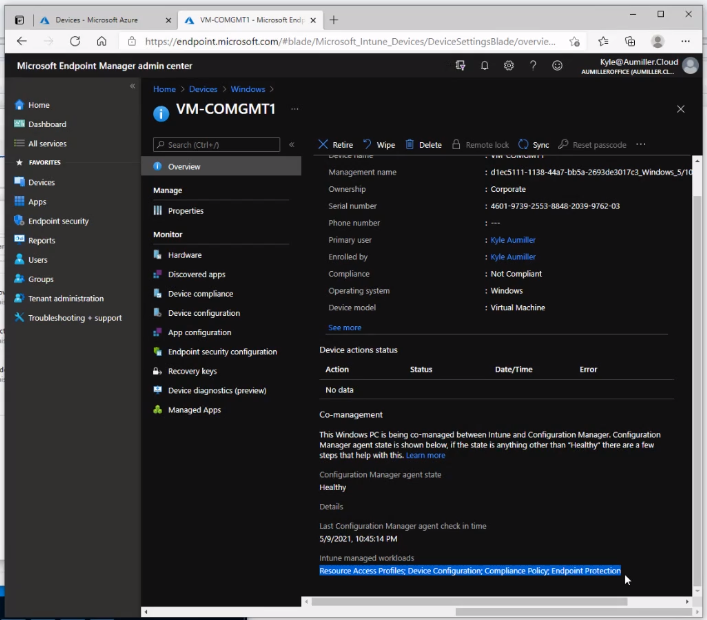
These I find crucial for if you have compliance policy that’s not applying to a device. You can come on here and actually validate from here that the compliance policy is in fact applying to this device.
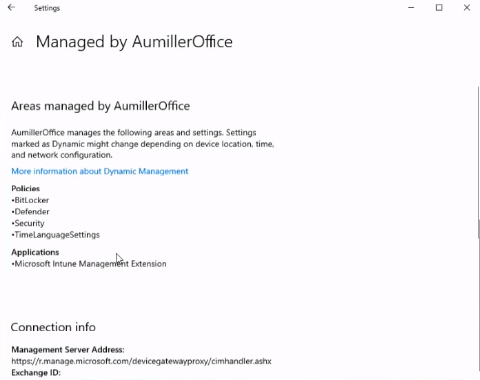
The next option is if you’re looking for the way a device is configured. If you go look at Device Settings, this will list your domains and you can see areas that Intune is applying policies.
There’s also an option to sync. If you were manually forced a sync over on the device, you can do that as well.
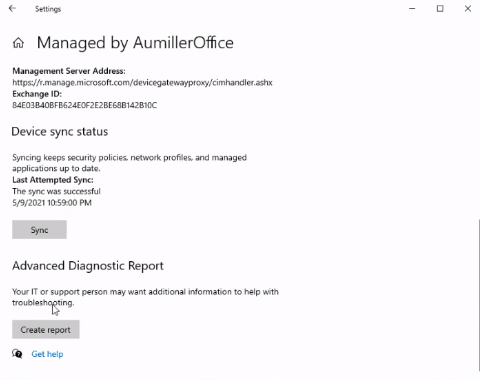
From here, you can create a report. Once you run the report, navigate to C:\Users\Public\Documents. There’ll be an MTM diagnostics folder. In this you can see:
- The device name
- The operating system
- The OS version
- What type of CPU you’re running on
- Any policies that are applied to this device
This information is helpful whenever you’re looking at troubleshooting. Or if you want to find out exactly what policies are applied to a device, you can also take a look at it in this report.
