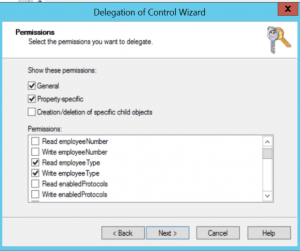
Last time we were talking about tracking Users and allowing updating of users attributes with what computers they were using. This time we will be looking at computers and track logins. We will be using a GPO and a login script to track logins and capture computer information, and then allow the computer object to update the following attributes. EmployeeType, Company, Department, Title, TelephoneNumber, EmployeeNumber, Division, SN, GivenName, TelephoneAssistant, Assistant, and IPAddress.
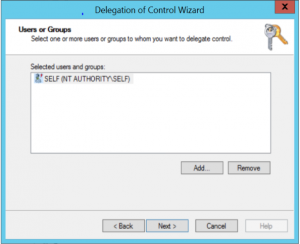
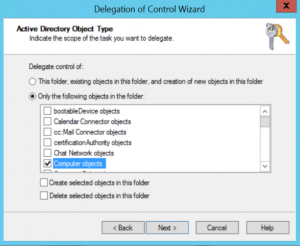
Using the Delegation Wizard to configure Self the ability to update Computer objects attributes above.
The script gathers the following information via WMI and updates the computer objects attributes with the following information.
slastuser, slasttime, biosbrand, compmodel, biosver, biosservicetag, compcpu, compram, compsystemtype, CompdomainroleRole, strlastboot,compOSInstall, and strIPAddress.
The script maps the WMI information to the following AD Computer attributes.
EmployeeType = slastuser & ” on ” & slasttime
Company = biosbrand
Department = compmodel
Title = biosver
TelephoneNumber = biosservicetag
EmployeeNumber = compcpu
Division = compram
SN = compsystemtype
GivenName = CompdomainroleRole
TelephoneAssistant = strlastboot
Assistant = compOSInstall
textEncodedORAddress = strIPAddress
Come back next time when we use a HTA to do some reporting on the Who, What, and Where.